Magereport
Magereport is a great online tool which scans websites that are running Magento and generates a report detailing which security patches and measurements they have installed and which they are missing.
We use Magereport in a number of situations, such as when a new lead comes through, either via phone or email, or if we come across a potential client running Magento. The instructions below will go over the process of running Magereport as well as what to do when we discover that a site has missing patches. * Note: Make sure you're using Wappalyzer in order to determine which site is using Magento.
Using Magereport.¶
Head over to Magereport with the website that you'd like to check opened up in another tab. Copy the website URL and paste it into the URL field on the left hand side of the screen, shown below.
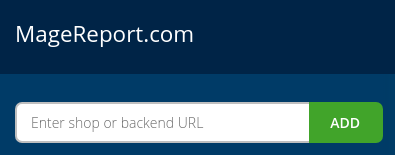
Then simply click "Add" to begin the scan.
The page will start to scan the website that you've entered, and begin loading the report. When it's done, you will see several boxes appear. Each represent a security patch, but may be different colours.
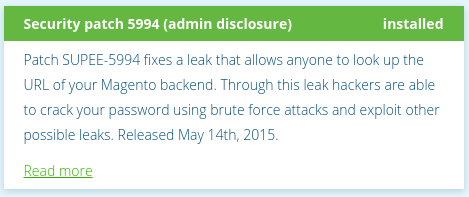
- Green: This indicates that the patch/security measure has been installed and required no further attention.
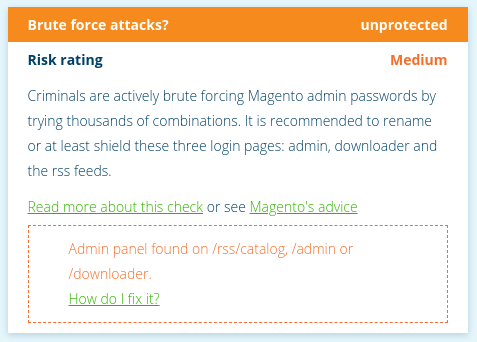
- Amber: This colour indicates that the represented security patch or measure isn't installed and poses a medium risk rating. Although it's not as severe as a high risk rating, it should still be addressed as soon as possible.
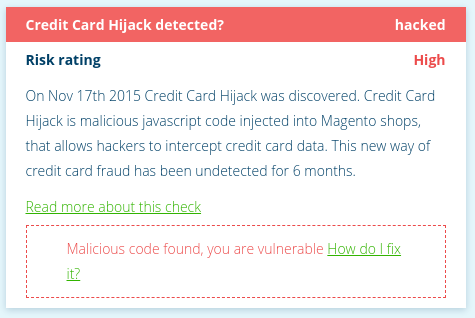
- Red: This colour indicated that the represented security patch or measure isn't installed and poses a high risk rating. These are of top priority, as failing to patch these can very likely result in a security breach within the site and should be addressed immediately.
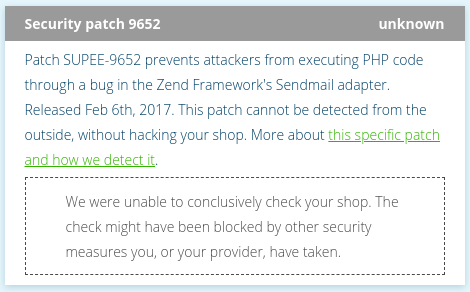
- Grey: Boxes that are highlighted in grey represent patches that Magereport was unable to scan for. As it says in the description box, it may be blocked by other security measures that either the owner or their host providers have put in place.
Now that we have the full report, we can reach out to the owner of the site and inform that of their holes in their security.
Reporting Magereport's Findings¶
When reaching out the the owner of the website, we want to emphasize that missing security patches isn't something that should be taken lightly. I lay out the patches in the email in the following way; providing a brief description of the patch, the date it was released (where applicable) and it's risk rating, such as the following examples down below.
- SUPEE-9797: Not installed. Released May 31st 2017. High risk rating.
- Brute Force Attacks: Unprotected against. Medium risk rating.
- Credit Card Hijack: Hacked! "Credit Card Hijack" discovered November 17th 2015. High risk rating.
Keep in mind that most of these patches are detailed in the "Quoting Guide" with time estimates. If one is missing and you need to quote a time, then feel free to ask some of the developers for an estimate instead.